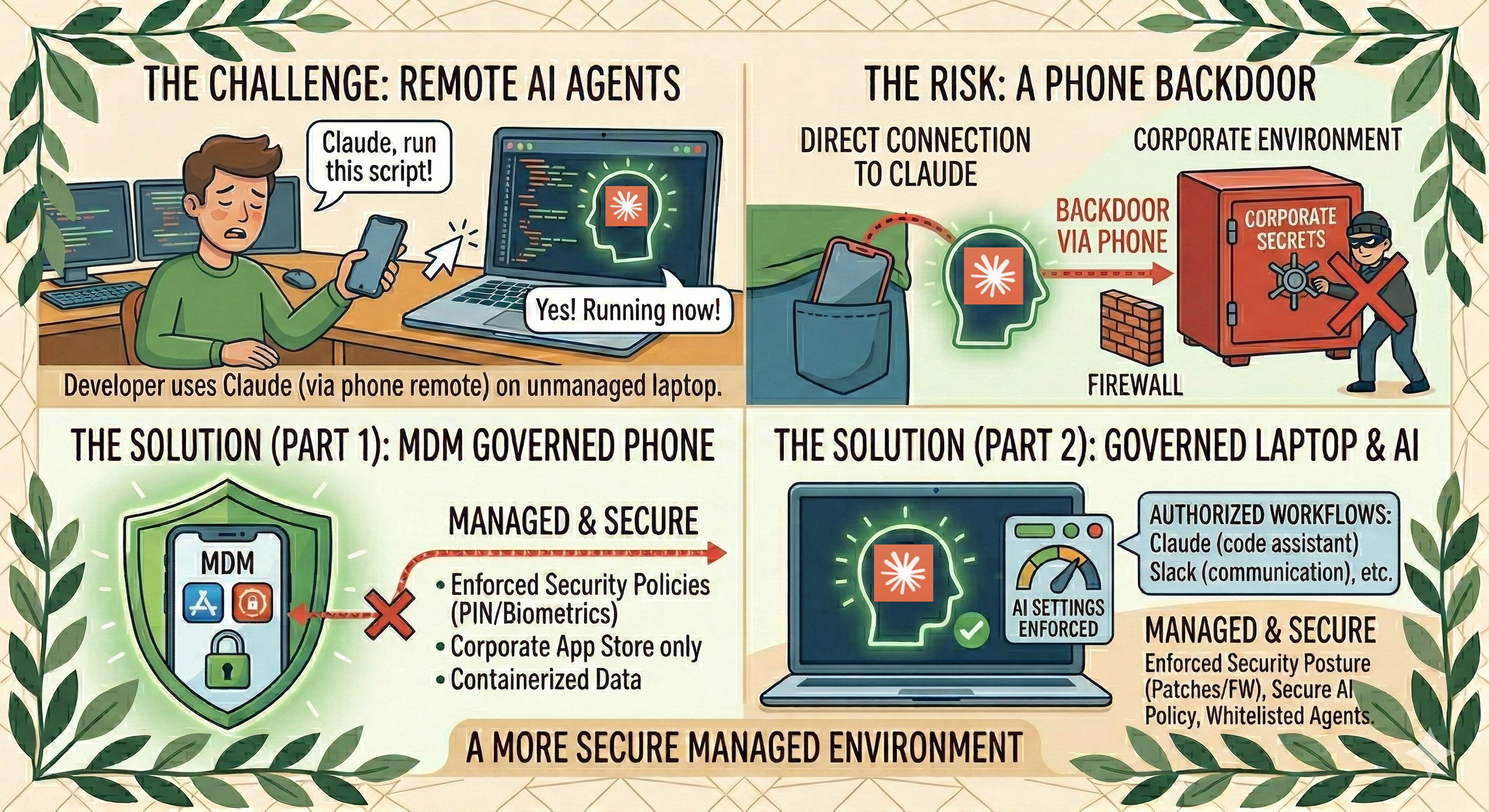
A new feature Anthropic recently released called “remote control” marks a major shift in how engineering teams operate. Develoeprs have always used a relatively closed environment. It is a place where code was written, tested locally, and then pushed to a central server. This is no longer true. This new capability, when enabled, changes that dynamic by allowing a developer to start a session on their laptop and then to control that terminal session from any mobile device or a web browser, bypassing existing SASE and DLP protections.
While this is great for productivity, it essentially places a remote shell on every machine where the tool is active. This creates a new path into the enterprise that security teams must understand. If your organization is not monitoring these connections, you are essentially blind to a new attack surface that exists on every engineer’s desk.
Claude Remote Control relies on an outbound connection to Anthropic servers. When a developer starts the remote control process, the local agent creates a reverse tunnel, allowing the tool to function through corporate firewalls and SASE without any manual configuration or open ports. This outbound-only model means a persistent pathway is established from the laptop to a third-party server, and onto a mobile device you have little control over.
Why MDM Is More Important Than Ever
Because the remote control feature allows a phone to command a laptop, the security of that phone is now an extension of the corporate network. If an employee uses a personal device to control their work machine, a compromise of the phone could lead to a compromise of the workstation. The best way to handle this is by using Mobile Device Management to place the Claude application within a secure container on the device that keeps corporate apps and data separate from personal content. This ensures that the sessions used for development are protected by encryption and strong authentication. Using a managed enclave approach ensures that the remote control feature is only used on devices that meet the company’s safety standards.
Managing Claude Code Itself Is Also Critical
The management of the developer laptop is just as important as the management of the mobile device. Organizations on Enterprise plans can use server-managed settings to enforce consistent standards for every engineer. These settings are at the top of the configuration list and cannot be changed by the individual user. This allows a company to disable risky features or create blocklists for sensitive files. For example, you can prevent the AI from reading SSH keys, which are digital credentials used to access servers, or environment variables that might contain secrets. By using these server-managed settings for teams, IT leaders can ensure that every installation of the tool follows the same security rules without relying on manual setup by each developer. Another reason to manage these tools centrally is the ability to collect telemetry data. Claude Code supports OpenTelemetry, which is an open standard for capturing this type of data across different systems. By exporting this telemetry to a central monitoring stack or AI Control Plane, an enterprise can see exactly what is happening across its entire fleet of AI agents. This includes tracking the cost of sessions and the number of tokens being used, as well as what tools and MCP are being called. Monitoring these metrics can help identify unusual patterns, such as an agent that is suddenly reading a large number of files or attempting to access restricted areas of the network.
Managing Claude For Observability and Governance
An AI gateway is a core piece of enterprise AI architecture that acts as a central infrastructure layer for all AI traffic. Using a gateway provides a single, secure entry point where policies can be enforced uniformly. This invisible backbone for AI agents allows for better observability and ensures that every interaction is logged for audit purposes. It also simplifies the networking requirements by centralizing the attack surface and providing a clear path for all AI-related data, and also allows AI agents to route and point to different models without changing the The most advanced way to govern these systems is through an AI control plane. A control plane is a management layer that is responsible for the discovery, policy, and monitoring of all AI agents in an environment. While a gateway handles the traffic, the control plane manages the rules and the state of the AI workforce. It provides a live registry of every agent and tool, which helps IT teams discover unauthorized tools that might be running on the network. An AI control plane can also automate remediation, such as stopping a session if an agent starts acting outside of its allowed boundaries. This level of control is necessary as we move toward a future where AI agents take autonomous actions on behalf of employees.
Conclusion: You Must Accelerate AI Governance Now, Not In Six Months
Ultimately, the goal is to build a governance framework that works at the speed of AI. By using managed enclaves, server-managed settings, and an AI control plane, an enterprise can create a secure environment for innovation. This infrastructure ensures that as developers get more powerful tools, the organization keeps the visibility and control needed to protect its most valuable data. The remote terminal feature is a great example of how development is changing, and the right architecture will ensure that these changes lead to better outcomes rather than new risks.
